- Youtube channel (UA): https://www.youtube.com/channel/UCqquOw2m2QF_EjcyxVwIYyQ
Saturday 1 October 2022
"Analysis of cyberweapons" course
- Youtube channel (UA): https://www.youtube.com/channel/UCqquOw2m2QF_EjcyxVwIYyQ
Monday 4 April 2022
Russian SaintBear Group Attacked Ukrainian Government Agencies Using GraphSteel & GrimPlant malware
Summary
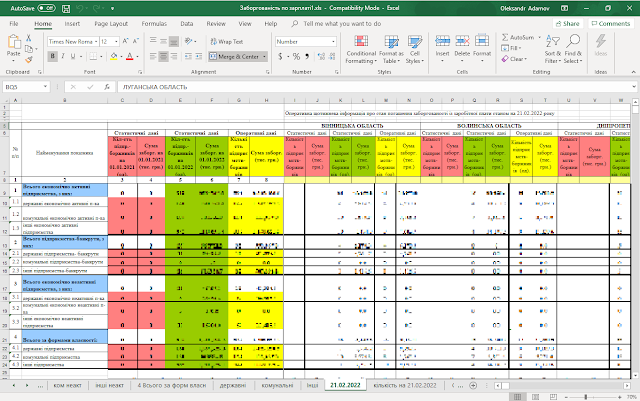
Name: ‘Заборгованість по зарплаті.xls’
Discovered in March 2022
Was used in attacks against Ukrainian government agencies
Used to download GraphSteel and GrimPlant (a.k.a. Elephant) malware
Spreads via phishing emails as ‘.xls’ file with malicious VisualBasic script
‘.xls’ file contains the encoded payload
Extracted file has PE64 format and written in Golang, downloads one file from the remote server
The downloaded file is PE64 and written in Golang. It downloads GraphSteel and GrimPlant malware.
The attack has been attributed to UAC-0056 also known as SaintBear, UNC2589, and TA471 which is known to attack Ukraine and Georgia since 2021.
Thursday 17 March 2022
Analysis of CaddyWiper
Summary
Name: CaddyWiper
Discovered in March 2022
Was used in a targeted attack in Ukraine
Deployed via Microsoft Active Directory GPO
Corrupts files and disk partitions
PE32 sample written in C++
Compiled on the same day when it was deployed on targeted systems in Ukraine
Wednesday 26 January 2022
Analysis of WhisperGate
Summary of the attack
Name: WhisperGate
Discovered in January 2022
Used in a targeted attack against the Ukrainian government websites on the 14th of January, 2022
Overwrites the contents of files with the fixed number of bytes
Rewrites MBR, corrupts victims’ files, downloads and drops its own files
Corrupted files have a random 4-byte extension
Comes with 2 stages, PE64 written in C++ and .NET application with fake digital signatures
The third stage is .NET DLL, which is downloaded at runtime
Friday 2 October 2020
Reinforcement Learning for Anti-Ransomware Testing
ML models have recommended themselves as a powerful tool for cyberdefense. AI/ML is heavily used in antiviruses (EDR), Next-Gen Firewalls, and SIEM (SOAR) solutions to solve the classification problem as well as to discover anomalous behavior that may indicate a presence of an attacker with the help of Supervised and Unsupervised Learning. Deep Learning helps to filter spam emails and mark fake news to protect users against disinformation [1].
Thursday 26 March 2020
AI and Cybersecurity. Part 4 - Clustering URLs
In Part 3, we tried to apply the feature scaling and dimensionality reduction techniques to the dataset with phishing and benign URLs. As a result, we were able to clearly see the distribution of URLs between two classes based on four attributes: registrar, country, lifetime, and protocol.
But what if we don’t have labels (phishing and benign) for the Internet links in the beginning. Will ML still work to detect phishing attacks? In this case, we may come to unsupervised learning, in particular, clustering. Clustering enables grouping objects of unknown classes according to common features so that we do not need labeled data for a training set.